This video is of a NON-XENON install. Be sure to follow the point changes in the image below the video for XENON consoles!
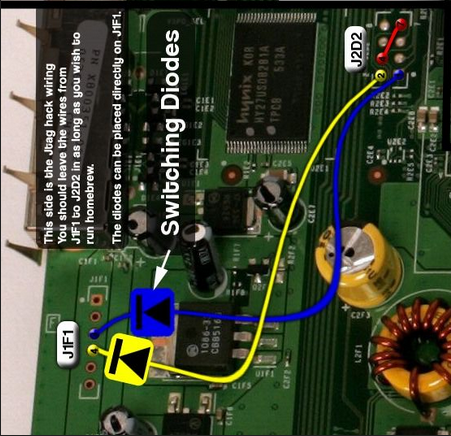
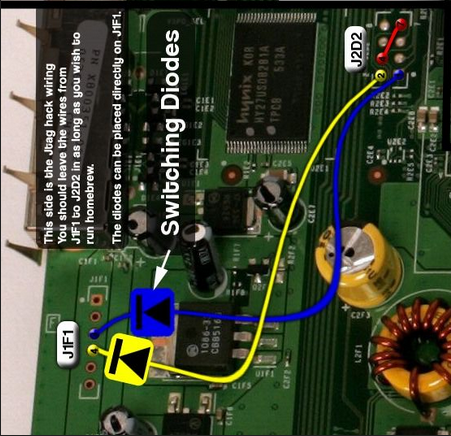
Use this wire layout for XENON's - it's the only change from the video!
My first successfull tutorial video ever... over 400,000 views now.
I'll be improving this by doing a 2017 update, but for now I'm just linking the original video.
The techniques in this video are still valid and going strong in 2017. Assuming you can find an exploitable console on dash 7371 or before, this method absolutely still works!
Within this video (at about the 2:10 mark) I state this is a NON-XENON video, and that is absolutely true. HOWEVER, if you look at the reference image below, it is of the XENON style wiring. So if you do what this video says, and just substitue the wiring from the picture below - you'll be good to go!
Use this wire layout for XENON's - it's the only change from the video!